Tax Season Scam Alert Microsoft Spots Malware Hidden in PDFs and QR Codes
Cybercriminals are exploiting tax season anxiety with sophisticated phishing attacks, Microsoft warns. These campaigns use convincing tax-themed emails containing malicious PDFs and QR codes designed to deliver malware and swipe unsuspecting victims' login information.
Heads up, everyone! Microsoft is sounding the alarm about a surge in phishing attacks that are using tax season as bait. These scams are designed to sneak malware onto your computer and steal your login details.
According to a report Microsoft shared with The Hacker News, these campaigns are getting sneaky. They're using URL shorteners, QR codes hidden in attachments, and even hiding behind legitimate services to avoid being detected. Think file-hosting sites and even business profile pages.
RaccoonO365: The Phishing-as-a-Service Culprit
A key element in these attacks? Many lead to phishing pages powered by a "phishing-as-a-service" (PhaaS) platform called RaccoonO365. This e-crime platform first popped up on the radar in late 2024.
But it doesn't stop there. These attacks are also delivering remote access trojans (RATs) like Remcos RAT. Plus, other nasty bits of malware and post-exploitation tools such as Latrodectus, AHKBot, GuLoader, and BruteRatel C4 (BRc4) are being spread.
Storm-0249: The Usual Suspect
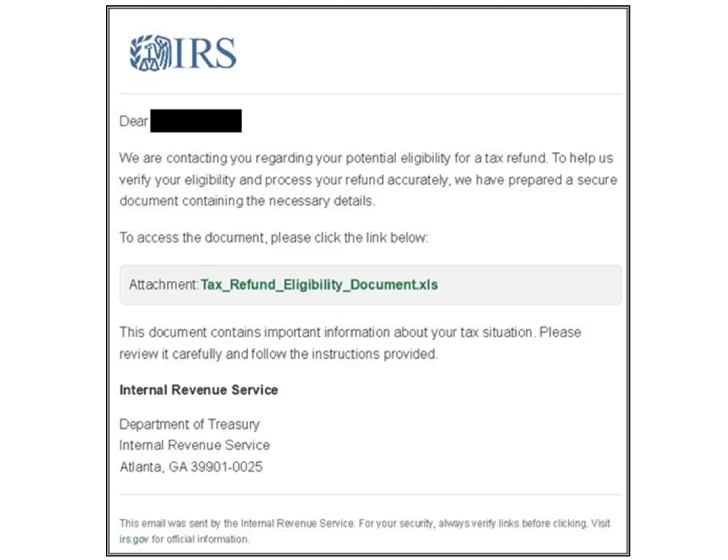
Microsoft flagged one specific campaign from February 6, 2025, that targeted the U.S. with hundreds of emails. The goal? To deliver BRc4 and Latrodectus ahead of tax season. This activity is linked to Storm-0249, a known initial access broker with a history of distributing malware like BazaLoader, IcedID, Bumblebee, and Emotet.
The trick involves PDF attachments containing links that redirect you to a shortened URL (using Rebrandly). This ultimately leads to a fake Docusign page where you're prompted to download or view a document.
Microsoft explains: "When users clicked the Download button on the landing page, the outcome depended on whether their system and IP address were allowed to access the next stage based on filtering rules set up by the threat actor."
If you're deemed a worthy target, you get a JavaScript file that downloads a Microsoft Software Installer (MSI) for BRc4, which then paves the way for Latrodectus. If not, you're sent to a harmless PDF document from royalegroupnyc[.]com.
QR Codes and Fake Login Pages: Another Tactic
Microsoft also discovered a second campaign (February 12-28, 2025) targeting over 2,300 organizations in the U.S., particularly in engineering, IT, and consulting. These emails were often blank, except for a PDF attachment with a QR code. This code leads to a link associated with RaccoonO365, mimicking Microsoft 365 login pages to steal your credentials.
It's clear these campaigns are varied. Tax-themed phishing emails are also spreading other malware families like AHKBot and GuLoader.
AHKBot infections have been found to direct users to malicious Excel files. If you open these files and enable macros, they download and run an MSI file to launch an AutoHotKey script. This script then grabs screenshots from your computer and sends them to a remote server.
The GuLoader campaign tries to trick you into clicking a URL in a PDF attachment, which downloads a ZIP file.
Microsoft explains, "The ZIP file contained various .lnk files set up to mimic tax documents. If launched by the user, the .lnk file uses PowerShell to download a PDF and a .bat file. The .bat file in turn downloaded the GuLoader executable, which then installed Remcos."
This all follows a previous warning from Microsoft about another Storm-0249 campaign that used fake Windows 11 Pro download pages to deliver an updated version of the Latrodectus loader malware via the BruteRatel red-teaming tool.
According to Microsoft on X, "The threat actor likely used Facebook to drive traffic to the fake Windows 11 Pro download pages, as we observed Facebook referrer URLs in multiple cases."
"Latrodectus 1.9, the malware's latest evolution first observed in February 2025, reintroduced the scheduled task for persistence and added command 23, enabling the execution of Windows commands via 'cmd.exe /c .'"
And, of course, we're also seeing a rise in campaigns using QR codes in phishing documents to hide malicious URLs, leading to widespread credential theft, especially in Europe and the U.S.
Palo Alto Networks Unit 42 notes, "Analysis of the URLs extracted from the QR codes in these campaigns reveals that attackers typically avoid including URLs that directly point to the phishing domain. Instead, they often use URL redirection mechanisms or exploit open redirects on legitimate websites."
These warnings come amidst a flurry of other phishing and social engineering attacks:
- Using the "browser-in-the-browser" (BitB) technique to serve fake browser pop-ups, tricking Counter-Strike 2 players into entering their Steam credentials.
- Using information-stealing malware to hijack MailChimp accounts for bulk email spam.
- Using SVG files to bypass spam filters and redirect to fake Microsoft login pages.
- Using trusted collaboration services (Adobe, DocuSign, Dropbox, Canva, Zoho) to bypass security and steal credentials.
- Using streaming services to hide threats.




