Outlaw Hackers Exploit Weak SSH Security to Hijack Linux Servers for Crypto Mining
A notorious hacking group known as Outlaw, also tracked as Dota, is actively brute-forcing SSH servers with poor security practices to install cryptocurrency mining malware. Researchers are warning that this self-spreading botnet poses a significant threat to Linux-based systems.

Security researchers have uncovered a sneaky cryptocurrency mining botnet called Outlaw (also known as Dota). This nasty piece of malware spreads automatically, targeting SSH servers that are using weak passwords.
Elastic Security Labs dropped a report on Tuesday, explaining that "Outlaw is a Linux malware that uses SSH brute-force attacks, cryptocurrency mining, and worm-like spreading to infect and stay in control of systems." You can read their full analysis here.
The name "Outlaw" also refers to the group of hackers behind the malware, believed to be from Romania. They're not the only ones in the cryptojacking game. Other groups making waves include 8220, Keksec (aka Kek Security), Kinsing, and TeamTNT. Check out this article for more on those groups.
Outlaw has been active since at least late 2018. This crew breaks into SSH servers by guessing passwords, using that access to explore the system, and then making sure they can get back in by adding their own SSH keys to the "authorized_keys" file. More details on their early activity here.
How Outlaw Attacks
These attackers use a multi-step process. First, they use a shell script (named "tddwrt7s.sh") to download an archive file ("dota3.tar.gz"). This file is unpacked to start the cryptocurrency miner. They also try to cover their tracks, removing signs of past infections and even shutting down rival miners (and their own old ones!). Read more about their attack chain.
One key feature of Outlaw is its self-spreading ability. It can scan for other vulnerable systems running SSH and try to break into them, creating a botnet. The brute-force module gets a list of targets from a command-and-control (C2) server, keeping the cycle going. More on their self-propagation techniques.
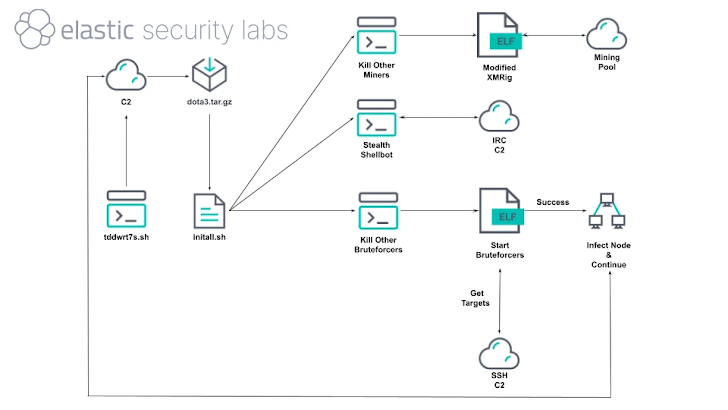
Sometimes, Outlaw also exploits older vulnerabilities in Linux and Unix systems, like CVE-2016-8655 and the infamous CVE-2016-5195 (aka Dirty COW). They also target systems with weak Telnet passwords. After getting in, they deploy SHELLBOT for remote control through an IRC channel.
SHELLBOT's Role
SHELLBOT lets the attackers run any shell command they want, download and run more malware, launch DDoS attacks, steal passwords, and grab sensitive data.
To make the mining more efficient, Outlaw figures out the CPU of the infected system and enables hugepages for all CPU cores to speed up memory access. It also uses a binary called kswap01 to keep the communication channel open with the attackers.
"Outlaw is still active even though it uses basic techniques like SSH brute-forcing, SSH key manipulation, and cron-based persistence," Elastic noted. "The malware uses modified XMRig miners, relies on IRC for command and control, and includes publicly available scripts for persistence and defense evasion."




