North Korean Hackers Use Fake Crypto Job Offers to Spread New Malware
A North Korean hacking group, known for past campaigns like Contagious Interview, is now using bogus job offers in the cryptocurrency industry to infect victims with a novel backdoor. Security researchers have dubbed the malware GolangGhost, a sophisticated program written in the Go programming language and capable of compromising both Windows and macOS systems. The hackers are employing a social engineering technique called 'ClickFix' to trick unsuspecting job seekers into downloading the malicious software.
Remember the "Contagious Interview" campaign? Well, the North Korean threat actors behind it are at it again. This time, they're using a sneaky tactic called ClickFix to trick job seekers in the crypto world. The goal? To install a previously unknown backdoor, dubbed GolangGhost, on both Windows and macOS machines.
French cybersecurity firm Sekoia calls this new campaign ClickFake Interview. The original Contagious Interview, which also goes by names like DeceptiveDevelopment and Famous Chollima, has been around since at least December 2022. It wasn't publicly known until late 2023, though.
"They're using real job interview websites to pull off the ClickFix trick and install backdoors," Sekoia researchers Amaury G., Coline Chavane, and Felix Aimé said. They're pointing the finger at the infamous Lazarus Group, a notorious group linked to North Korea's Reconnaissance General Bureau (RGB).
Here's a twist: this campaign is mainly targeting centralized finance companies. They're pretending to be companies like Coinbase, KuCoin, and Kraken. This is different from the group's usual attacks on decentralized finance (DeFi) entities.
Like Operation Dream Job, Contagious Interview uses fake job offers as bait. They lure in potential victims and trick them into downloading malware that can steal cryptocurrency and other sensitive information.
The hackers contact candidates on LinkedIn or X and ask them to prepare for a video interview. Then, they ask them to download a malicious videoconferencing app or open-source project, which kicks off the infection process.
Security researcher Taylor Monahan first exposed Lazarus Group's use of the ClickFix tactic in late 2024. The attacks lead to the deployment of FERRET malware, which then delivers the Golang backdoor.
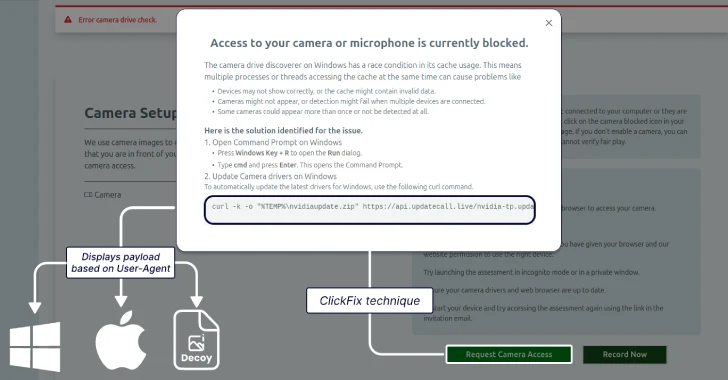
In this latest version of the campaign, victims are asked to visit a fake video interviewing service called Willo and complete a video assessment.
"The whole setup is designed to build trust," Sekoia explained. "Everything goes smoothly until the user is asked to enable their camera." That's when an error message pops up, saying the user needs to download a driver to fix the problem. That's where the ClickFix technique comes into play.
The instructions for enabling camera or microphone access depend on the operating system. On Windows, victims are told to open Command Prompt and run a curl command to execute a Visual Basic Script (VBS) file. This file then launches a batch script to run GolangGhost.
If the victim is using a macOS machine, they're asked to launch the Terminal app and run a curl command to execute a shell script. This script runs another shell script, which then executes a stealer module called FROSTYFERRET (aka ChromeUpdateAlert) and the backdoor.
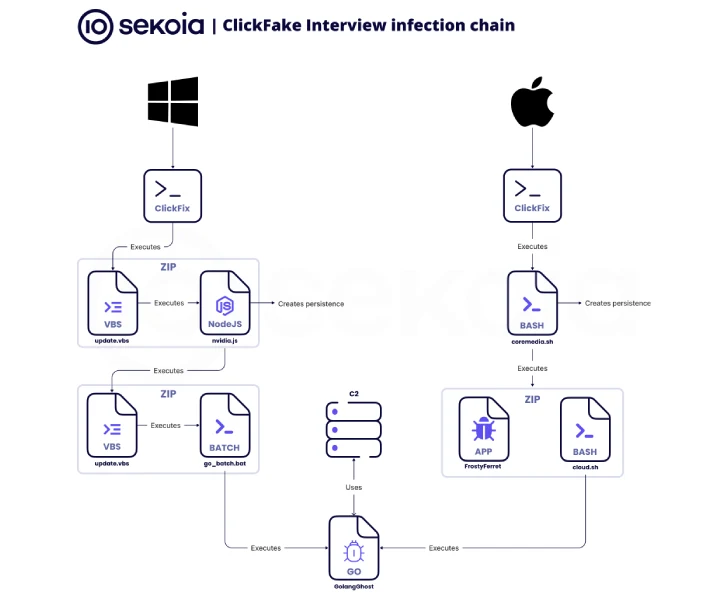
FROSTYFERRET displays a fake window claiming that Chrome needs access to the user's camera or microphone. It then asks for the system password. The entered information, whether it's correct or not, is sent to a Dropbox location. This likely means the attackers are trying to access the iCloud Keychain using the stolen password.
GolangGhost is designed for remote control and data theft. It can upload/download files, send host information, and steal web browser data.
"We found that the positions weren't related to technical software development profiles," Sekoia noted. "They're mainly management jobs focusing on business development, asset management, product development, or decentralized finance."
This is a big change from previous fake job interview campaigns linked to North Korea, which mainly targeted developers and software engineers.
North Korea IT Worker Scheme Expands to Europe
The Google Threat Intelligence Group (GTIG) has noticed a surge in the fraudulent IT worker scheme in Europe. This shows a significant expansion beyond the United States.
The IT worker activity involves North Korean nationals pretending to be legitimate remote workers to infiltrate companies and generate illegal revenue for Pyongyang, violating international sanctions.
Increased awareness and U.S. Justice Department indictments have led to a "global expansion of IT worker operations," according to Google. They've found several fake personas seeking jobs in Germany and Portugal.
These IT workers have also been working on projects in the United Kingdom related to web development, bot development, CMS development, and blockchain technology. They often lie about their identities, claiming to be from Italy, Japan, Malaysia, Singapore, Ukraine, the United States, and Vietnam.
The managed intelligence firm Nisos highlighted this tactic of IT workers posing as Vietnamese, Japanese, and Singaporean nationals early last month. They also pointed out their use of GitHub to create new personas or reuse portfolio content from old ones.
"IT workers in Europe were recruited through online platforms like Upwork, Telegram, and Freelancer," said Jamie Collier, Lead Threat Intelligence Advisor for Europe at GTIG said. "They were paid using cryptocurrency, TransferWise, and Payoneer, which hides the origin and destination of the funds."
Besides using local facilitators to get jobs, these insider threat operations seem to be seeing a rise in extortion attempts since October 2024, when the IT worker scheme became public.