Massive Login Scan Targets Palo Alto Networks GlobalProtect Gateways
A surge of suspicious login attempts is targeting Palo Alto Networks' PAN-OS GlobalProtect gateways, prompting cybersecurity alerts. Researchers have identified almost 24,000 distinct IP addresses involved in what appears to be a coordinated campaign to probe for vulnerabilities.

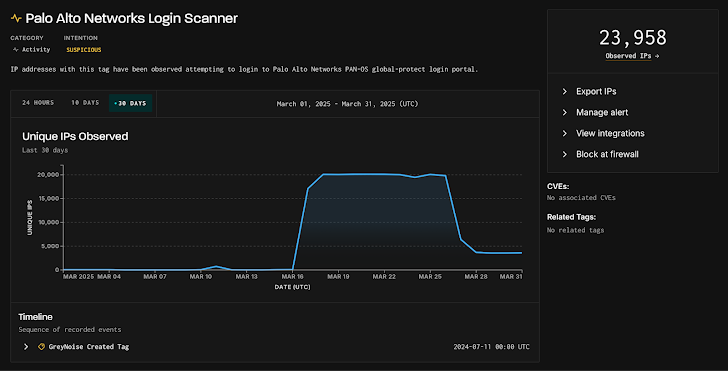
Cybersecurity researchers are raising the alarm about a recent surge in suspicious login scanning aimed at Palo Alto Networks PAN-OS GlobalProtect gateways. Get this: nearly 24,000 unique IP addresses have been trying to poke around these portals.
According to GreyNoise, a threat intelligence firm, this looks like a coordinated effort. They say it's likely a way to test network defenses and sniff out vulnerable systems, potentially setting the stage for future attacks.
This activity reportedly kicked off around March 17, 2025, with almost 20,000 unique IP addresses involved daily before things calmed down around March 26. At one point, they counted a whopping 23,958 unique IP addresses. Interestingly, only a small fraction – about 154 – have been flagged as outright malicious.
Where's all this traffic coming from? The United States and Canada seem to be the primary sources, followed by Finland, the Netherlands, and Russia. And the targets? Mostly systems in the U.S., U.K., Ireland, Russia, and Singapore.
The motive behind this scanning activity remains unclear. What *is* clear is that it suggests a systematic approach to probing networks, which could definitely lead to trouble down the road.
Bob Rudis, VP of Data Science at GreyNoise, notes a worrying trend. "Over the past 18 to 24 months, we've observed a consistent pattern of deliberate targeting of older vulnerabilities or well-worn attack and reconnaissance attempts against specific technologies," he explained. "These patterns often coincide with new vulnerabilities emerging 2 to 4 weeks later."
So, what should you do? If your organization uses internet-facing Palo Alto Networks products, now's the time to double-check and secure your login portals. Better safe than sorry!
We've reached out to Palo Alto Networks for their take on all this, and we'll update the story if we get a response.




