Lucid PhaaS Smishing Campaign Reaches Global Scale
A newly discovered phishing-as-a-service platform, dubbed Lucid, has been linked to a widespread smishing campaign impacting 169 organizations across 88 countries. The platform leverages both Apple's iMessage and Android's Rich Communication Services (RCS) to deliver convincing phishing messages, broadening its reach and potentially increasing its effectiveness.

A new phishing threat is making waves: a sophisticated Phishing-as-a-Service (PhaaS) platform called Lucid. It's been used to target a whopping 169 entities across 88 countries. What makes it different? It's leveraging smishing – phishing via SMS – through Apple's iMessage and Android's Rich Communication Services (RCS).
Lucid's key advantage is that it weaponizes legitimate communication channels. This allows it to slip past the usual SMS spam filters.
"This platform's scalable, subscription-based setup lets criminals run large-scale phishing campaigns, aiming to steal your credit card details for financial gain," says PRODAFT, a Swiss cybersecurity firm. They shared a technical report with The Hacker News.
According to PRODAFT, "Lucid exploits Apple iMessage and Android's RCS tech. By doing so, it avoids standard SMS spam defenses, boosting both delivery and success rates for these attacks."
The finger is being pointed at a Chinese-speaking group of hackers known as the XinXin group (also called Black Technology). They seem to be behind Lucid. Their main targets are in Europe, the UK, and the US. Their goal? To grab credit card info and your Personally Identifiable Information (PII).
But here's the kicker: the people running Lucid aren't new to this game. They've also created other PhaaS platforms, including Lighthouse and Darcula. Darcula has even been upgraded, letting criminals clone any brand's website for phishing.
The mastermind behind Lucid is reportedly a threat actor known as LARVA-242, a key player in the XinXin group.
The three platforms – Lucid, Lighthouse, and Darcula – show similarities in their templates, target selection, and attack methods. This points to a thriving underground market where Chinese-speaking actors use Telegram to peddle their malicious services on a subscription basis, all for profit.
These phishing campaigns often impersonate familiar entities like postal services, delivery companies, toll payment systems, and tax agencies. They use convincing templates to trick people into handing over sensitive details.
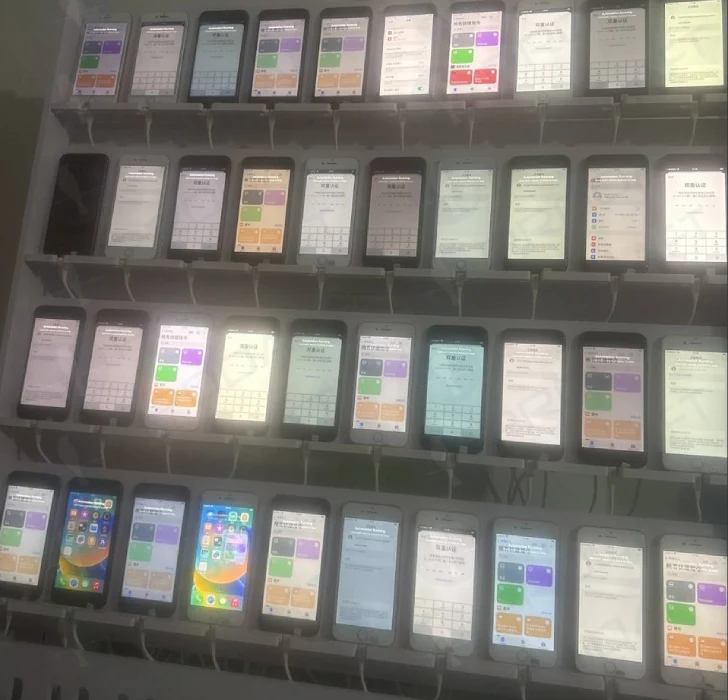
These large-scale operations are powered by iPhone farms and mobile device emulators, all running on Windows. They're used to send hundreds of thousands of scam messages, complete with fake links, in a coordinated manner. And where do they get the phone numbers? Think data breaches and cybercrime forums.
"To get around iMessage's link-clicking restrictions, they use 'please reply with Y' tactics to start a conversation," PRODAFT explains. "And to dodge Google's RCS filters, they constantly switch sending domains and numbers to avoid being detected."
"For iMessage," PRODAFT continues, "this involves creating temporary Apple IDs with fake display names. RCS exploitation takes advantage of inconsistencies in how carriers verify senders."
Besides providing automated tools to easily create customized phishing sites, these pages have advanced anti-detection features. This includes blocking IPs, filtering user agents, and using single-use URLs that expire quickly.
Lucid also allows users to track victim activity and record every interaction with the phishing links in real-time through a dashboard, letting them extract entered information. Credit card details are also put through extra verification steps. The dashboard itself is built using the open-source Webman PHP framework.
"The Lucid PhaaS panel shows a very organized network of Phishing-as-a-Service platforms run by Chinese-speaking threat actors, mainly the XinXin group," says PRODAFT.
According to the security firm, "The XinXin group develops and uses these tools, profiting from selling stolen credit card information. They also actively monitor and support the development of similar PhaaS services."
Interestingly, PRODAFT's findings are echoed by Palo Alto Networks Unit 42. They recently highlighted how certain threat actors are using the "com-" domain pattern to register over 10,000 domains for spreading SMS phishing scams through Apple iMessage.
This news comes as Barracuda warns of a "massive spike" in PhaaS attacks in early 2025 using Tycoon 2FA, EvilProxy, and Sneaky 2FA. These services accounted for 89%, 8%, and 3% of all PhaaS incidents, respectively.
"Phishing emails are the starting point for many attacks, from stealing credentials to financial fraud and ransomware," says Deerendra Prasad, a security researcher at Barracuda. "The platforms powering Phishing-as-a-Service are becoming more complex and harder to detect. This makes phishing attacks harder for security tools to spot and more damaging." said.




